Latest Cybersecurity News:
All you need to know about cyber security
Blockchain Cybersecurity Uses
Blockchain cybersecurity: A blockchain is a database in which data is stored as a series…
How to Create an Effective Cyber Security Data Protection Plan
Having effective cyber security data protection in place can help you save from the millions…
Latest Cybersecurity Attacks
What are the latest cybersecurity attacks today? Today, cybersecurity is a growing concern for every company. No…
Benefits of Security Automation
Organizations can reap a lot of benefits from security automation. Benefits of Security Automation It…
Top Reasons Why Cybersecurity Is Interesting
From competitive salaries to ever-evolving job descriptions, there are tons of reasons why cybersecurity is…
What is Cybersquatting?
Cybersquatting occurs when a domain name is registered to sell it to the owner of…
What is Mobile Device Security?
Mobile device security is the process of protecting mobile devices against cyber-attacks and unauthorized access….
Best Cybersecurity YouTube Channels
We are now living in a time where great cybersecurity content is freely available on…
Cloud Computing Security Threats in Mobile Banking
Among other industries, banking and finance face cloud computing security threats most commonly. This industry…
Cyber Security Salary: Highest Paying Jobs In Cyber Security
If you are pursuing careers in the field of cybersecurity, you might be concerned about…
Information Systems Security Officer
Learn more about the information systems security officer. What are their jobs, their responsibilities, and…
What is a Strong Password?
“A strong password is not easily guessed or cracked.” According to the National Institute of…
What is an Account Takeover Attack?
There are two types of account takeover attack. Password attacks are personalized attacks on a…
Advantages and Disadvantages of Automation Testing
What are the advantages and disadvantages of automation testing? Advantages and Disadvantages of Automation Testing Advantages: 1. Reduces Time and Cost: Automated tests are quicker to execute and require less time as compared to manual testing because human intervention is not required for execution and also no interpretation or analysis is required for reporting results which can be automated as well. 2.Enables Repeatability: Automated tests are repeatable. For example, they can be run any number of times with the…
5G Cybersecurity: What Are The Challenges?
Soon enough, we will see 5G take over the world. But not everything looks good. 5G cybersecurity challenges will also rise with it. True, there are lots of perks to 5G becoming mainstream. Faster download speed, lower latency, and bigger network capacity. But as with any other new technologies, challenges are always present. Especially in one of the biggest concerns in the digital world. Cybersecurity. So, what will 5G bring along with it? Will these be hard to…
Be Safe from Mobile Security Issues
With the convenience of mobile phones and gadgets come mobile security issues. However, you can keep yourself and your company’s network safe, if you practice healthy mobile security hygiene. Mobile Security Issues Safety Here are tips on how you can keep yourself safe from these mobile security issues. 1. Be wary of the apps you install. Take the time to research any apps you download or install on your device. For instance, if you want to download a game…
Choosing a Career in Cybersecurity or Cloud Computing
Are you torn between cybersecurity or cloud computing for your career path? This article will help you weigh the pros and cons of each field. By doing so, you can decide with field suits you best. What is Cybersecurity? The word “cybersecurity” is a combination of two words, cyber and security. Cybersecurity is the protection of computer data and systems connected to the internet. It has become an essential field for businesses and corporations today. However, this…
How to Automate Threat Hunting with Security Analytics?
The main goal of threat hunting is to find new unknown threats. Threat hunting is not just about finding the threats, but also discovering evidence of attacks and how the attackers are operating. Here are ways on how you can automate threat hunting with security analytics: 1. Using Security Analytics to automatically find new attacks 2. Using Security Analytics to automatically find the attackers 3. Using Security Analytics to automatically detect and track the attacker’s activities 4….
Cybersecurity Government Jobs Explained
What’s it really like to land one of the cybersecurity government jobs? Is it worth it? Find out the answers to those questions in this article. This resource is for individuals who want to work for the U.S. government. Pros & Cons Cybersecurity government jobs have many pros. For instance, your country truly needs you as there is a massive shortage of cyber experts. Moreover, you might enjoy the thought of working for the NSA or CIA….
Internet Of Things Cybersecurity (IoT)
Are you familiar with the internet of things cybersecurity (IoT)? Well, the development of this technology brought many benefits for us today. So, what exactly is IoT? What are the potential risks it brings? What Is The Internet Of Things Cybersecurity? Internet of Things or IoT is the idea of connecting any type of device to the internet. Today, individuals and businesses become more connected. Thus, increasing the opportunities for innovation.As a result, more objects and devices…
Steps in Building a Security Operation Center
A security operations center is a centralized unit that handles organizational and technical security challenges. Steps in Building a Security Operation Center 1. Develop your security operations center strategy. First, you must develop your strategy. What risks must you address? What is your organization’s security posture? Where do you want it to be in three to five years? What are your goals? Next, develop a plan for your security operation center. Then, consider the size and risk of your organization….
Global Industrial Cybersecurity Professional
GICSP or Global Industrial Cybersecurity Professional. This is a special and vendor-neutral certificate in ICS security. But, let us know more in this article. What Is Global Industrial Cybersecurity Professional? GICSP or Global Industrial Cyber Security Professional. This will be the next certificate in the GIAC group. It centers on the vital knowledge of handling private network assets. Further, GICSP is the only credential in the globe. That relies primarily on the cybersecurity issues of Industrial Control…
Remote Working Security Best Practices
Here are some remote working security best practices: Remote Working Security Best Practices Have the same level of security awareness Ensure that end users have the same level of security awareness in the remote office as they do in the central office. Make sure that they know to never give out their username and password to anyone (no matter how trustworthy they seem), and to be suspicious of links in emails. Never store sensitive data in publicly…
Biggest Cybersecurity Attacks 2018
2018 saw a series of malicious hacks and data breaches. In this article, let’s take a look at the biggest cybersecurity attacks 2018. Indeed, no one is safe from cybersecurity attacks. You are a prime target for hackers as long as you possess data. It doesn’t matter if your enterprise is in the private or public sector. It’s estimated hackers compromised over 4.5 billion records. Yet, that is just in the first half of 2018. That massive…
Modern Days Cyber Threats and Security
In our life, the Internet and computers have become inseparable. But, we should also know about cyber threats and security. Nowadays, by any means, we connect to the internet. Through a smartphone, tablet, or computer. Gadgets that we used for storing information. Also, in booking tickets, online banking, and shopping. As well as connecting to our friends and playing games. Technologies made our life easier. Networks today simplified the means of communication. Also, provided opportunities in almost…
How the Information Security Involves the Protection of Customers
While maintaining high cybersecurity measures protects the company itself. Information security involves the protection of customers as well. Why is this so? In this post, let us consider how information security also benefits customers. Why Information Security Involves the Protection of Customers The Internet offers consumers a lot of opportunities, such as the ability to connect with brands and businesses. Companies can benefit from these opportunities by building solid relationships with their customers. However, this is not possible…
5 Cloud Computing Advantages in the Workplace
Here are the cloud computing advantages that apply in the workplace. Despite the statistics pointing to the business efficiency, cost-benefits, and competitive advantages that cloud computing offers, a huge section of the corporate community continues to function without it. Some executives are cautious to commit to cloud computing solutions for their companies. As a result, we’d like to spend a few moments discussing the 5 commercial benefits of cloud computing. Cloud Computing Today As cloud technology has…
Who Are The Top Cybersecurity Companies In The World?
Discover the top cybersecurity companies in the world. Top Cybersecurity Global Companies McAfee McAfee tops the list as being the most renowned cybersecurity company in the market. This company has its headquarters in Santa Clara, California. The company began the business in 1987. Governments- McAfee provides cybersecurity solutions to different government entities around the globe. Most specifically, McAfee Global Threat Intelligence. This McAfee solution helps entities keep themselves one step ahead of malicious actors.Businesses- McAfee also provides…
Cybersecurity 101: All You Need To Know About Cybersecurity
Cybersecurity 101- what is cybersecurity? Also, why is it more important for most businesses today? Learn the basics of cybersecurity and how it affects you. What is Cybersecurity? Cybersecurity is a system used to protect computers, programs, and data from unauthorized use or attack. Moreover, cybersecurity is important because it helps protect our online lives and keeps us safe from hackers. Cybersecurity is a system used to protect computers, programs, and data from unauthorized use or attack. So cybersecurity…
What is Two-factor Authentication?
Two-factor authentication is a method of confirming a user’s claimed identity by utilizing something they know (such as a password) and something they have (a physical token or cell phone). It is commonly used in everyday life. For example, withdrawing money from an ATM requires something you know (your bank card PIN) and something you have (your bank card). Like all good security systems, two-factor authentication creates an additional barrier of protection that an attacker has to…
What to Include in an Incident Response Plan for Data Breach
Here are the elements that you should include in an incident response plan for the data breach. Key Elements in Incident Response Plan for Data Breach 1. Introduction It’s critical to have a thorough beginning that describes the aims, scope, and guiding principles. The aim of the plan (for example, a hospital’s plan should minimize downtime of critical services and loss of sensitive patient data) can serve as a guide for the rest of the document. The introduction should…
How Does Cloud Computing Google Services Work?
Cloud computing Google services is one of the most popular cloud computing services available today. Google’s platform in cloud services is a collection of Google’s public cloud computing services. The platform comprises a variety of Google-hosted services for computation, storage, and application development. In this post, we will learn more about Google cloud computing services, and how it works. What is Cloud Computing Google Services? Cloud computing is a technology that enables the access of applications or…
List Of Computer Security
Here is the list of computer security types, threats, also vulnerabilities, and many more. So this is a list of anything that could add some knowledge about computer security. Introduction About Computer Security Computer security or also know as IT security is the safety of the information security system. This serves as a shield from the following: damage to the hardware also softwarethe leak of the informationalso, the disorder of the services. Moreover, it covered the following:…
Basic Cybersecurity Guidelines for Social Media Use
Learn the basic cybersecurity guidelines for using social media in businesses. This article teaches employees the basic cybersecurity guidelines to use when using social media in businesses. It outlines what kinds of information you should keep private, what information should be under restriction, and how employees can avoid privacy breaches. Cybersecurity in Social Media Use: What Businesses Need to Know This article covers the basics of using social media in a way that is safe from hackers and other…
News feed from the web
all about cyber security
US Fleet Cyber Command, US Navy Space Command welcome new VADM > United States Space …
FORT GEORGE G. MEADE, Md., Sept. 18, 2020 —. Vice Adm. Ross Myers relieved Vice Adm. Timothy “T.J.” White as…
Return to Office: Cybersecurity experts seeing more malware on devices of employees
Concept of cyber crime, businesswoman using computer and show malware screen that comes with email, hack password from bank accounts…
Cooley Hires Cyber/Data/Privacy Leader and Team in Europe
Leading cyber/data/privacy partner Patrick Van Eecke joins Cooley in the firm’s Brussels office. read source
New to Cyber Summit 2021
We’re opening this virtual Summit to the community! Register now for FREE. Two days of in-depth and interactive cyber security…
Cyber Attacks Are Spiking – Is Your Hotel Prepared?
Cyber threats are rampant within this digitally-driven era. In the wake of the coronavirus pandemic, experts are calling for enhanced…
Cyber Focus: Food manufacturing
Cyber Focus: Food manufacturing … The recent ransomware attack on the Brazilian meat processing company, JBS S.A. attributed to REvil…
WATCH LIVE: Colonial Pipeline CEO testifies on cyber attack as US recovers ransom payment
“For financially motivated cyber criminals, especially those presumably located overseas, cutting off access to revenue is one of the most…
Locating people in Capitol siege should be a ‘slam dunk,’ says cyber security expert
A local cyber security expert says the volume of images from that day should make it easy to locate them….
When requests for help turn into cyber bullying: Inside a few popular Kerala FB groups
For many online groups on Malayalam social media, cyber bullying disguised as ‘advice’ or ‘genuine concern’ has been a major…
Black Friday in-store shopping dropped 52.1% as online sales broke records. Will Cyber Monday …
Black Friday in-store shopping dropped 52.1% as online sales broke records. Will Cyber Monday follow? Kelly Tyko. USA TODAY. read…
rep lieu calls for action following russian cyber attack
REP LIEU CALLS FOR ACTION FOLLOWING RUSSIAN CYBER ATTACK. December 15, 2020. Press Release. WASHINGTON – Today … read source
REVEZ Corporation Sees Strong Demand for Stellar Cyber, the World’s First Open XDR …
To date, customers from the region, such as Akati Sekurity, depend on the Stellar Cyber platform for providing fast, automated…
Cyber Process Engineer
Provide appropriate challenge to risk acceptance. Cyber Engineering Reporting, Education and Awareness. Advocate for improvements in Security … read source
Baltimore County Schools To Close Monday, Tuesday Due To Ransomware Cyber Attack
The school system said daily updates will be provided at 5 p.m. moving forward. There is still no word on…
Cyber attack on US government may have started earlier than initially thought – US senator
WASHINGTON (Reuters) – The unprecedented cyber attack on U.S. government agencies reported this month may have started earlier than last…
Cyber Readiness Institute and US Department of Homeland Security Partner to Help US …
Cyber Readiness Institute and U.S. Department of Homeland Security Partner to Help U.S. Businesses Secure Remote Workforces. WASHINGTON, DC, … read…
Outcomes-Based Security
There’s a better way to deliver cybersecurity services, but it requires seeing things from the customer’s perspective. When a business…
NZX interrupted but trading continues after last week’s cyber attacks
The stock exchange has suffered several interruptions this morning, but trading has continued. NZX. Photo: NZX / Supplied. The NZX…
Data for 700M LinkedIn Users Posted for Sale in Cyber-Underground – NDRdaily
Daily insights on Network Detection and Response, Network Visibility and Cyber Resilience … read source
Friendly Planet Travel
read source
Cyber is the new Cold War, and AI is the arms race
The use of AI to analyze these massive amounts of cyber data and capabilities is growing exponentially. In 2016, when…
The Get Cyber Resilient Show Episode #34
We talked about the problem with the perception of vendors in cyber resilience and get Jason’s insights, since you have…
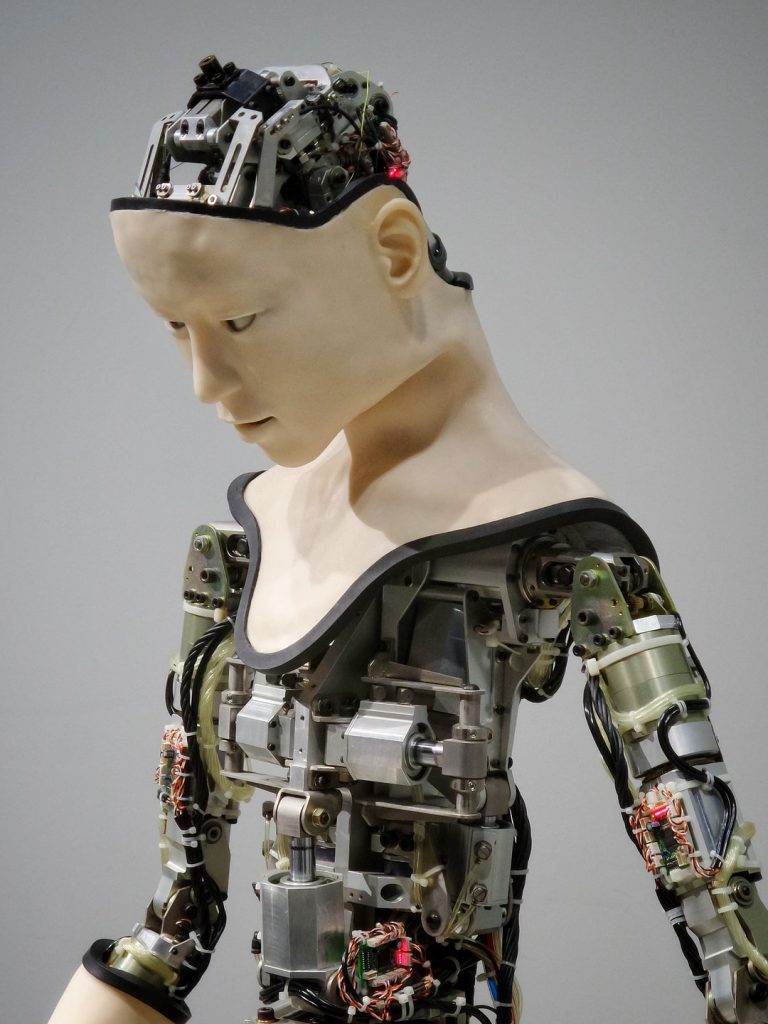
Cyber Security in Robotic Market Trend, Industry Analysis, COVID-19 Impact, Growth Rate and …
Cyber Security in Robotic Market Trend, Industry Analysis, COVID-19 Impact, Growth Rate and Future Forecast 2020-2026 | Top Players: McAfee, ……
Preventing cyber attacks this holiday
HUNTINGTON, W.Va. (WSAZ) -. People are online now more than ever before. The internet is the all-in-one destination for work,…
Darktrace Version 5 Released For General Availability To Protect Cloud And Remote Workforce
Powered by self-learning Cyber AI, the Darktrace Immune System works by learning the normal ‘pattern of life’ of an organization,…
Burns & Wilcox launches new personal cyber insurance offering
Burns & Wilcox has launched a new cyber protection product line designed with the cybersecurity of individuals, families and households…
Global Artificial Intelligence (AI) in Cyber Security Market Expected to reach growth rate of XX …
Global Artificial Intelligence (AI) in Cyber Security Market: An Evaluation of the Scope. This extensively researched report presentation on global ……
Army mints new cyber research and development agreement with Estonia
He noted the agreement is in preliminary stages and researchers haven’t identified specific projects yet. Andri Rebane, director of the…
Jamil Jaffer: The US needs to do more to deter cyber attacks
Former chief counsel and senior adviser for the Senate Foreign Relations Committee Jamil Jaffer weighs in on ‘America’s News HQ.’…
Biden Warns Putin of Cyber Retaliation
If, in fact, they violate these basic norms, we will respond in a cyber way,” Biden said at a post-summit…
“Cyber 101” Free Courses Tackle Cybersecurity Issues – The Times of Houma/Thibodaux
The Institute for Industry-Education Collaboration and Nicholls State University presents “Cyber 101” courses to tackle the issue of cybersecurity. read…